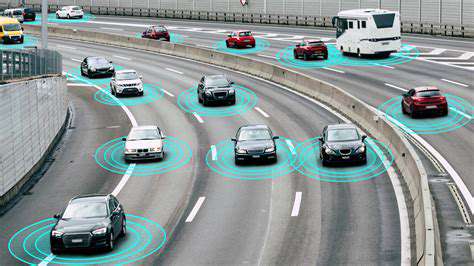
The proliferation of connected cars has ushered in a new era, transforming the automotive landscape and generating an unprecedented volume of data. This data encompasses a wide range of information, from vehicle performance metrics and driver behavior to location tracking and even interior environment details. This wealth of data, while offering potential benefits, also introduces significant security challenges that need careful consideration. The sheer amount of information collected by these vehicles, constantly flowing from sensors and onboard systems, presents both opportunities and vulnerabilities for malicious actors.
From sophisticated diagnostic tools to real-time performance monitoring, this data stream fuels advancements in various fields. This includes everything from optimizing manufacturing processes to improving driver safety and enhancing the overall driving experience. However, the ease with which this data can be collected also underscores the importance of robust security measures to protect it from unauthorized access and exploitation.
Security Risks in the Connected Car Ecosystem
The interconnected nature of modern vehicles exposes them to a range of potential security threats. Cybercriminals could exploit vulnerabilities in the vehicle's communication systems to gain unauthorized access to sensitive information, potentially leading to significant harm. This includes not only theft of valuable personal data but also the potential for malicious control of critical vehicle functions, such as braking, steering, or even the engine.
Data breaches in connected cars could have devastating consequences. Imagine a scenario where hackers gain control of a fleet of vehicles, leading to widespread accidents or even deliberate attacks. Furthermore, the potential for misuse of location data, coupled with other personal information, raises concerns about privacy violations and identity theft. These risks necessitate a proactive approach to security, focusing on robust encryption, secure communication protocols, and rigorous testing of connected car systems.
Protecting the Data Flow: Strategies for a Secure Future
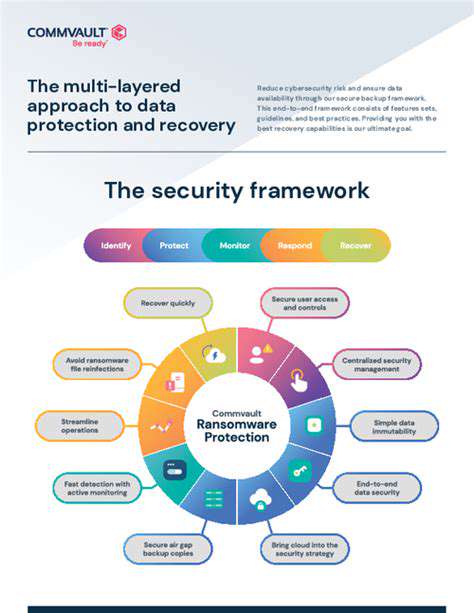
Securing the vast amount of data generated by connected cars requires a multi-faceted approach. This includes implementing strong encryption protocols throughout the entire communication chain, from the vehicle to the cloud. Furthermore, regular security audits and vulnerability assessments are crucial to identify and address potential weaknesses in the systems. Robust authentication mechanisms are essential to verify the identity of users and devices interacting with the vehicle's systems.
Investing in advanced cybersecurity technologies, such as intrusion detection systems and secure software development practices, is also vital. Furthermore, promoting industry-wide standards and regulations for connected car security will be essential to ensure a uniform level of protection. Ultimately, a collaborative effort between manufacturers, regulators, and cybersecurity experts is required to create a secure and reliable connected car ecosystem that protects sensitive data and prevents potential harm.
Protecting Your Data: A Multi-Layered Approach
Implementing Robust Security Measures
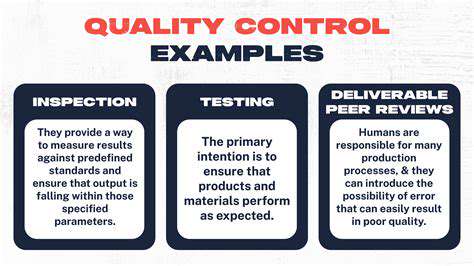
Protecting sensitive data requires a multi-faceted approach, encompassing various layers of security. A strong foundation involves implementing robust security protocols across all systems and platforms where data is stored and transmitted. This includes utilizing strong encryption methods for data at rest and in transit. Implementing these measures can significantly reduce the risk of unauthorized access and data breaches.
Furthermore, access controls should be meticulously defined and enforced. This involves granting users only the necessary permissions to access specific data. Regular audits of access privileges are crucial to identify and address any potential vulnerabilities and ensure compliance with data protection regulations.
Data Loss Prevention (DLP) Strategies
Data Loss Prevention (DLP) strategies are essential for preventing sensitive data from leaving the organization's control. These strategies involve implementing policies and technologies to monitor and control data movement, both internally and externally. Implementing DLP solutions can help organizations identify and prevent data leaks, protecting valuable information from unauthorized access.
This includes educating employees about the importance of data security and implementing policies that govern data handling. This education should cover topics like identifying potential threats, avoiding phishing scams, and secure data disposal procedures. These measures can significantly reduce the risk of accidental or malicious data loss.
Physical Security Considerations
Physical security measures are often overlooked but are equally important in safeguarding data. Protecting physical access to data centers, servers, and other sensitive locations is crucial. This includes implementing secure access control systems, surveillance cameras, and regular security audits of physical premises. Physical security measures are vital for preventing unauthorized access to critical infrastructure, thereby ensuring data safety.
Regular security assessments of physical environments are essential to identify and mitigate potential security risks. This includes evaluating the security of building access points, surveillance systems, and emergency response plans. Thorough assessments can help ensure that physical security measures are up-to-date and effective in protecting sensitive data.
Employee Training and Awareness
Employee training and awareness programs play a critical role in maintaining a strong security posture. Educating employees about the importance of data security, common threats like phishing attempts, and the organization's data protection policies is essential. This training equips employees with the knowledge and skills to recognize and report potential security incidents, reducing the risk of data breaches.
Regularly updated and comprehensive training materials should cover various aspects of data security, including the identification of malicious emails, the appropriate use of company devices, and the importance of secure passwords. This proactive approach fosters a culture of data security awareness, which is crucial for protecting sensitive information.
Driver Responsibilities and Safe Driving Practices
Driver Responsibilities in Connected Cars
Drivers of connected vehicles have a crucial role to play in ensuring the security of their data and the safety of themselves and others on the road. Understanding the potential risks associated with connected car technology is paramount. This includes being aware of the various data points collected by the vehicle and how this data might be vulnerable to unauthorized access or misuse. Drivers should proactively manage their vehicle's settings and applications, ensuring that only trusted and necessary data is shared with the vehicle's system and third-party services. Safe driving practices, like avoiding distractions from in-car entertainment systems and maintaining focus on the road, are even more critical in connected vehicles, as the temptation to multitask can be significantly higher.
Drivers need to be vigilant about potential vulnerabilities and actively seek out information about the security features and privacy policies of their vehicles and connected apps. Regular updates, both to the vehicle's software and the connected apps, are often necessary to patch security flaws. Taking the time to understand these aspects is not just about the security of the vehicle's data but about maintaining a safe driving environment. It's a shared responsibility, and drivers must be aware of their role in protecting their own data and that of others.
Safe Driving Practices Enhanced by Connected Car Technology
While connected car technology offers many benefits, such as advanced safety features, drivers must remain vigilant about safe driving practices. These features, including adaptive cruise control, lane departure warnings, and automatic emergency braking, can enhance safety, but they should not replace the driver's responsibility for maintaining situational awareness and reacting appropriately to changing road conditions. Drivers should not become overly reliant on automated systems, always remaining attentive and prepared to intervene if the system fails or provides inaccurate information.
A key aspect of safe driving in connected cars is avoiding distractions. The availability of in-car entertainment systems, navigation apps, and other connected features can be tempting, but drivers must prioritize their focus on the road. Constant engagement with these features can lead to dangerous lapses in attention, negatively impacting reaction times and increasing the risk of accidents. Drivers should utilize these features thoughtfully and avoid operating them while driving to maintain optimal driving safety. Proper use of connected car technology is essential for maximizing the benefits of advanced features and maintaining safe driving habits.
Drivers should familiarize themselves with the limitations and potential inaccuracies of the connected car technology. For example, weather conditions, road construction, or other external factors can affect the accuracy of certain data inputs. It's vital for drivers to maintain a healthy skepticism and not solely rely on the data provided by the vehicle. The system should be viewed as an aid, not a replacement for the driver's judgment and decision-making skills.
Understanding the limitations of connected car technology is crucial for safe driving. By supplementing the system's information with their own situational awareness, drivers can use connected car features responsibly and safely.
Careful monitoring of the vehicle's systems and timely action in case of malfunctions are critical to maintaining safe driving practices. Appropriate maintenance and updates are necessary for the continued functionality and security of the connected car features. Drivers should be informed about the vehicle's features and proactively address any alerts or warnings to prevent potential issues.
The Future of Connected Car Security

The Rise of Cybersecurity Threats
The increasing connectivity of automobiles presents a compelling opportunity for enhanced convenience and efficiency, but it also introduces significant cybersecurity risks. Connected cars, with their embedded systems and communication networks, are vulnerable to various malicious attacks. These attacks can range from simple disruptions of onboard systems to more sophisticated intrusions that compromise sensitive data and control of the vehicle. This vulnerability is amplified by the growing reliance on cloud-based services for vehicle updates and maintenance. This connectivity creates a potential avenue for attackers to exploit vulnerabilities in these systems.
Cybersecurity breaches in connected vehicles can have far-reaching consequences. Imagine a situation where an attacker gains control of a vehicle's braking or steering systems, potentially leading to catastrophic accidents. The potential for theft and unauthorized access to personal data stored within the vehicle is also a critical concern. Protecting this sensitive data and maintaining the integrity of vehicle systems is paramount for the safe and reliable operation of connected vehicles.
Enhanced Security Measures and Protocols
Addressing the growing cybersecurity risks in connected cars requires a multi-faceted approach. Automotive manufacturers are increasingly implementing robust security measures, including the development of secure communication protocols, encryption techniques, and advanced intrusion detection systems. Implementing these technologies will help to safeguard vehicle systems against malicious attacks. Furthermore, ongoing research and development in areas like AI-powered threat detection and response systems are essential to combat emerging threats.
Regular software updates and patches are critical for maintaining the security of connected car systems. These updates address known vulnerabilities and enhance the overall resilience of the vehicle against cyberattacks. Automotive manufacturers need to prioritize secure software development practices to reduce the risk of vulnerabilities being exploited. Furthermore, establishing clear and consistent security protocols for data transmission and storage is crucial for protecting sensitive information.
Collaboration between manufacturers, researchers, and regulatory bodies is essential to foster a secure ecosystem for connected cars. Open communication and knowledge sharing will help to accelerate the development and deployment of effective security solutions. This collective effort is vital to ensure that connected vehicles are protected from evolving threats.
Future Trends and Predictions
The future of connected car security will likely be shaped by advancements in artificial intelligence (AI) and machine learning (ML). AI-powered systems can analyze vast amounts of data to identify and respond to potential cyber threats in real-time, significantly improving the overall security posture of connected vehicles. This proactive approach to security will be essential in mitigating the risks associated with increasingly complex and interconnected systems.
A focus on zero-trust security models will be increasingly important. This approach assumes that no user or device should be trusted implicitly, requiring continuous verification and authentication. This philosophy will be critical in securing the communication channels and data exchange between the vehicle and external services. By implementing these strategies, the industry can strive towards a more secure and reliable future for connected cars.